Combine Physical and Virtual Appliances in a Private Cloud
ipSpace.net » Case Studies » Combine Physical and Virtual Appliances in a Private Cloud
Central IT department of the government of Genovia is building a new private cloud which will consolidate workloads currently being run at satellite data centers throughout various ministries.
The new private cloud should offer centralized security, quick application deployment capabilities, and easy integration of existing application stacks that are using a variety of firewalls and load balancers from numerous vendors.
The document describes a summary of design challenges sent by readers of ipSpace.net blog and discussed in numerous ExpertExpress engagements. It’s based on real-life queries and network designs but does not represent an actual customer network. Complete document is available as downloadable PDF to ipSpace.net subscribers.
Existing Network Services Design
All current data centers (run by the central IT department and various ministries) use traditional approaches to network services deployment (see Figure 1):
- A pair of central firewalls and load balancers;
- Small number of security zones implemented with VLAN-based subnets;
- Security zones shared by multiple applications.
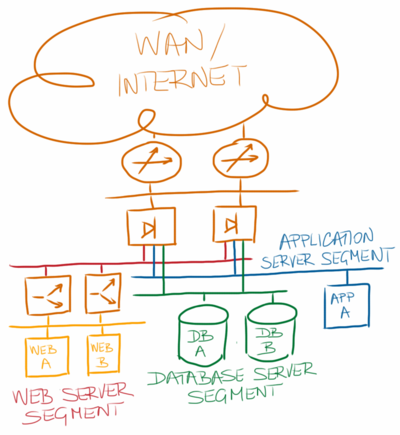
Figure 1: Centralized network services implemented with physical appliances
The central IT department provides Internet connectivity to the whole government; other data centers connect to the private WAN network as shown in Figure 2.
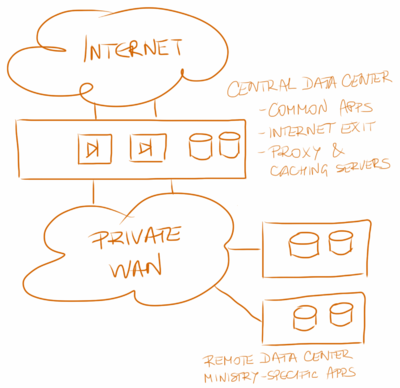
Figure 2: Centralized network services implemented with physical appliances
Security Requirements
Applications run within the existing data centers have highly varying security requirements. Most of them need some sort of network-layer protection; some of them require deep packet inspection or application-level firewalls that have been implemented with products from numerous vendors (each ministry or department used to have its own purchasing processes).
Most application stacks rely on data stored in internal databases or in the central database server (resident in the central data center); some applications need access to third-party data reachable over the Internet or tightly-controlled extranet connected to the private WAN network (see Figure 3).
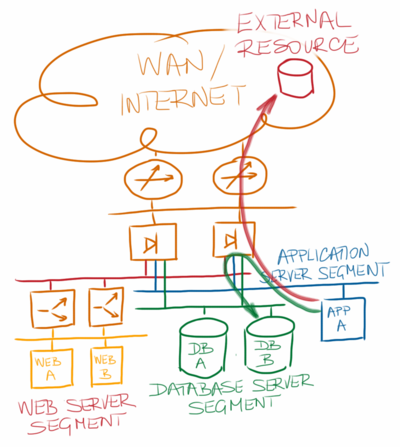
Figure 3: Applications accessing external resources
Migrating the high-security applications into the security zones that have already been established within the central data center is obviously out of question – some of these applications are not allowed to coexist in the same security zone with any other workload. The number of security zones in the consolidated data center will thus drastically increase, more so if the cloud architects decide to make each application an independent tenant with its own set of security zones.[1]
Private Cloud Infrastructure
The consolidated private cloud infrastructure will be implemented with the minimum possible variability of the physical hardware to minimize the hardware maintenance costs, effectively implementing the cloud-as-an-appliance design[2].
The cloud architecture team decided to virtualize the whole infrastructure, including large bare-metal servers, which will be implemented as a single VM running on a dedicated physical server, and network services appliances, which will be implemented with open-source or commercial products in VM format.
There’s More
The rest of the case study covers these following topics:
- Network Services Implementation Options
- Network Tapping and IDS
- Load Balancing
- Network-Level Firewalls
- Deep Packet Inspection and Application-Level Firewalls
- SSL and VPN Termination
- The Reality Intervenes
Notes
- Make every application an independent tenant
http://blog.ipspace.net/2013/11/make-every-application-independent.html - Cloud-as-an-Appliance design
http://blog.ipspace.net/2013/07/cloud-as-appliance-design.html
Get the complete document
Complete case study, including design and deployment guidelines and sample configuration snippets is available to ipSpace.net subscribers. Select the Case studies tab after logging into the webinar management system.
Case Studies
- BGP Convergence Optimization
- BGP Routing in DMVPN Access Network
- Designing a Private Cloud Network Infrastructure
- External Routing with Layer-2 Data Center Interconnect (DCI)
- Integrating Internet VPN with MPLS VPN WAN
- Redundant Data Center Internet Connectivity
- Redundant Server-to-Network Connectivity
- Replacing the Central Firewall
- Scale-Out Private Cloud Infrastructure
Webinar roadmaps
- Cloud Computing and Networking
- Containers and Docker
- Data Center Infrastructure
- Internetworking Technologies
- IP version 6
- Network Automation
- Network Security
- Network Virtualization
- Networking Fundamentals
- Software Defined Networking (SDN)
- Software-Defined Data Centers (SDDC)
- Virtual Private Networks
